Extracting BitLocker keys with Volatility (PoC)
**Update 2016-03-13:**There is more detail, including a link to a plugin for Volatility in the more recent article Recovering BitLocker Keys on Windows 8.1 and 10 .
This article is mainly to document a proof-of-concept Volatility plugin to extract the Full Volume Encryption Key (FVEK) from a memory dump of a Bitlocker-enabled Windows machine. The tools already exist to do this and potentially assist in gaining access to an encrypted machine, provided you have Windows running (Example scenario may be an encrypted laptop with TPM-only Bitlocker protection for which you do not have credentials).
But firstly, a few notes…
Note 1: This is a little side-project I am using to learn more about writing Volatility plugins, and memory forensics in general. It is not finished but I am writing this article to gather some of my thoughts into a more coherent format and for motivation to finish. As such, I haven’t posted the code to the plugin as quite frankly it is the coding equivalent of duct tape and cable ties and I’m not happy with it. Over the next month or so I will write up Part 2 and include the code – In the meantime though simply email me if you have questions.
Note 2: This is not a vulnerability and is nothing new – It is simply the way any Full Disk Encryption system works and all (E.G. Apple FileVault, or the now-defunct Truecrypt and its forks) can have the same issue. For performance reasons it is generally necessary to keep the decryption key in memory, otherwise you end up needing to first access the key before accessing the data which tends to add an overhead.
If your Bitlocker implementation requires a higher level of security to completely mitigate cold-boot attacks, consider following Microsofts own best practice and using an authentication mechanism such as TPM + PIN, which will go a long way to thwarting cold-boot attacks (But will not, however, prevent other attacks such as FireWire DMA attacks…).
There are many, many factors which come into executing a successful cold-boot attack and realistically it isn’t high up there on the list of risks for most people.
**Note 3:**This is currently only valid for Bitlocker in Windows 7 and possibly Vista (untested) – I believe the implementation has changed after Win 7 and this is not applicable, but I will be looking into this.
Anyway – Now a bit of an explanation about how Bitlocker works – Although there are much more comprehensive resources out there on the Internet.
In Windows 7 Bitlocker uses an AES Cascading Block Cipher of either 128 or 256 bit length, optionally with a diffuser, and has 4 modes of operation:
- AES 128-bit + Elephant Diffuser (Default)
- AES 128-bit (without diffuser)
- AES 256-bit + Elephant Diffuser
- AES 256-bit (without diffuser)
Note: The Elephant Diffuser has been removed in Windows 8 and above with no replacement.
The key used to encrypt/decrypt the data itself (Each sector is encrypted individually) is known as the Full Volume Encryption Key (FVEK) and is stored in the disk metadata, itself encrypted by another key called the Volume Master Key (VMK). The VMK is in turn encrypted using one of Bitlockers protectors: This may be the Trusted Platform Module (TPM), a recovery password, certificate or a combination of either. In the case where Bitlocker is “Suspended” a cleartext key is used to encrypt the VMK and offers no protection whatsoever.
Bitlocker Full Volume Encryption Keys are always 512-bits in length regardless of mode, and as mentioned the key we are after is the decrypted copy of the FVEK stored in RAM. Thanks to the excellent research from Jesse Kornblum we know that the AES key schedule is stored in RAM and we know what to look for.
Using Microsoft’s documentation and this excellent prior research we know that on Windows 7 the AES Full Volume Encryption Key (FVEK) is stored in a memory pool identified by the pool tag FVEc (Used to identify cryptographic pool allocations). The Bitlocker mode is also identified as well as the TWEAK key used by the Elephant Diffuser, if in use.
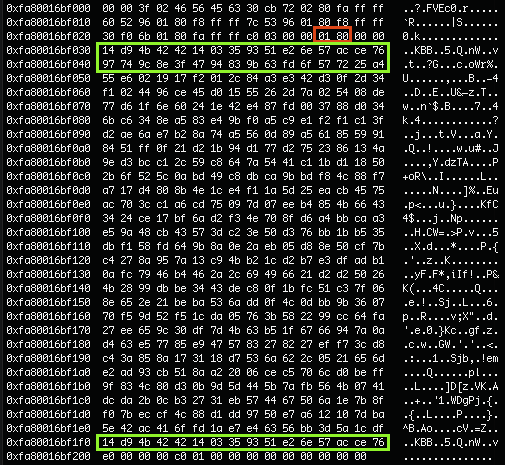
- Red: Bitlocker mode (8001 = AES 256 with Diffuser)
- Green: FVEK
- TWEAK not shown
To test this I setup a VM running Windows 7 and enabled Bitlocker (USB passthrough to the VM to store the key). Whilst it was running, I dumped a copy of the VM’s RAM to analyse. This is much, much easier than using a physical machine – but good enough to test a proof of concept as we know we are going to get a reliable RAM dump, whereas dumping RAM from a physical machine is more likely to introduce errors.
Once we have obtained a memory dump we can use Volatility’s pool scanning capabilities to search for the appropriate pool tag. Although it is relatively easy to pull out the data manually I wanted to write a plugin which identifies the relevant data and prints it out nicely (As a side note – aeskeyfind will also locate the FVEK if you know what to look for).
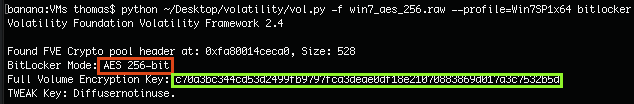
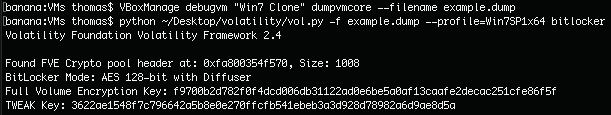
The plugin is really simple and is essentially just a basic pool scanner which searches for the FVEc pool tag specifically, then identifies the Bitlocker mode and outputs the appropriate FVEK and TWEAK (if applicable). Here are examples of the testing output for several Bitlocker modes:
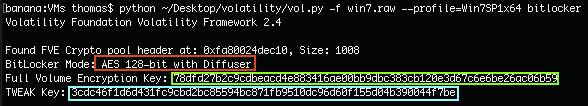 AES 128-bit with Diffuser (Default mode)
AES 128-bit with Diffuser (Default mode)
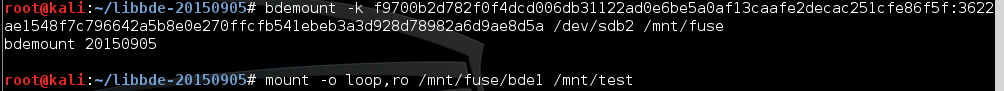
To test this and ensure we actually have the correct keys I can simply attach the encrypted disk to a Linux VM and use libbde to mount the disk with the FVEK ( + TWEAK if required).
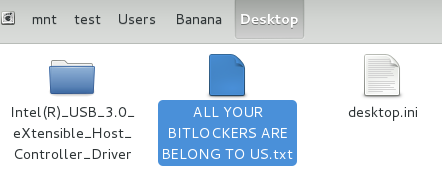
Firstly, we create a test file on the desktop of the VM:
![First, an identifying file on the VM Desktop.] (GHOST_URL/content/images/2015/11/desktop111.png)
First, an identifying file on the VM Desktop.
Next we take a memory dump and use the Volatility plugin to grab the required keys:
Then we use libbde to mount the volume, using the FVEK + TWEAK:
No complaints there, lets check it out…
Great success! High-fives all around! We have successfully accessed a Bitlocker encrypted volume using Volatility to extract the keys from a memory dump. Though, I must stress this is nothing new nor is it really anything impressive.
Update: The initial hacked together code may be found here (For historical purposes…). However, I have cleaned up and improved some of the code in another plugin which can be found in the more recent article Recovering BitLocker Keys on Windows 8.1 and 10.
As usual, feel free to get in touch with any feedback.